Connection to DriversCloud Create a DriversCloud.com account Reset your DriversCloud.com password Account migration
What is a Kill switch and why activate it?
In simple terms, a Kill switch is a unique feature that is activated when the Internet connection is lost.
When you accidentally disconnect from a VPN network, your computer immediately acquires a specific IP address. If you don't have a kill switch, your online activities can be exposed.
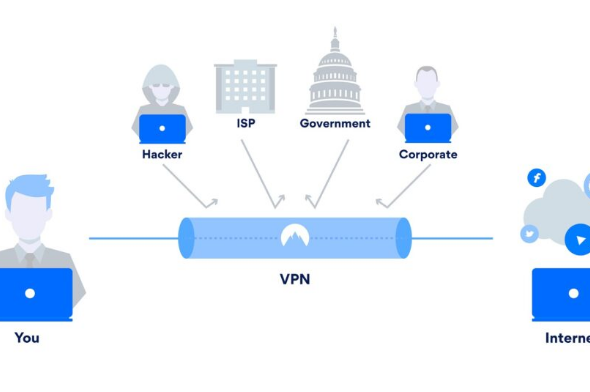
VPN, the basics to know about this software
This is the definition of a VPN this is a virtual private network that protects the privacy of its users online by hiding their IP address and routing their traffic through a secure "tunnel". However, no matter how good and reliable the VPN service is, connectivity issues can arise, leaving users' security exposed. That's where a kill switch comes in. The Kill switch is one of the best tools available for users concerned about their online privacy. If the VPN connection suddenly fails, a Kill switch automatically blocks all connections to the Internet until the user can reconnect to the VPN server.
Without this mechanism, the traffic will go back through the ISP. This means that the user's IP address and all of their activities would be exposed, as if there was no VPN in the first place. Most users don't need this level of security. But for those who are concerned about their security, such as journalists trying to expose government corruption or other forms of crime, this feature is essential.
When the Kill switch is enabled
Depending on the VPN software, this option can be enabled or disabled depending on the preferences of each user. In general, it is recommended to keep it enabled, otherwise there will be certain times when network traffic will be routed through the ISP, exposing your data. The Kill switch is persistent: when a user decides to change the country of the server, it stays on. The kill switch can be activated in each of these cases:
- When the VPN server has connectivity problems and disconnects the user.
- In case the network connection is not very good (e.g. Wi-Fi with a weak signal), this function will not allow to re-establish the connection via the IP address assigned by the Internet service provider.
Types of Kill switch
There are two types of Kill switch available to VPN users:
- System-level: this type completely shuts down all network activity until the VPN connection is re-established or the user reboots their network adapter. Applications that use a system-level shutdown switch only have an on/off button.
- Application level: users can choose which applications they want to disconnect from the Internet (browsers, email clients, chat applications, torrent clients, etc).
The second type can be detrimental for users who are not sure which applications are running in the background and will try to connect to the Internet. You may even see software that does not require an active Internet connection to run, but has an automatic update service. If this application connects via the user's public IP address, your data could be compromised.
How does a Kill switch VPN work?
An example of a Kill switch mechanism is one based on firewall rules. A firewall is responsible for blocking unauthorized connections to the system, although exceptions can be added so that users can still access many trusted services.
The Kill switch uses this feature to redirect all network traffic through the VPN tunnel. It also blocks all connections when there is no network connectivity, eliminating the risk of all traffic going through the IP address assigned by the ISP and exposing your online identity.
These are the steps by which this mechanism works:
- You create a backup of your current firewall rules before connecting to the VPN.
- All outbound network connections are disabled.
- The following exceptions are added as firewall rules: the local IP address of the tunnel (the IP address assigned to the device by the VPN), the IP address of the VPN server (which will be displayed on the IP discovery pages), and the VPN provider's web page.
Upon complete disconnection from the VPN, the aforementioned firewall rules are removed and the backup made in the first step is restored. This will allow the user to browse the Internet using the IP address assigned by his provider.